Tor Darknet
What is Tor? The dark web is the part of the deep web that's only accessible through a special browser: the Tor browser. Also called thedarknet, this. All it takes is downloading darknet software. Swensen said the most common dark web networks are Tor, I2P, and Freenet, but Tor is. By E Jardine 2024 Cited by 106 Online anonymity-granting systems such as The Onion Router (Tor) network can be used for both good and ill. The Dark Web is possible only. The Dark Net is real. An anonymous and often criminal arena that exists in the secret, far reaches of the Web, some use it to manage. Researchers at Bat Blue Networks today released a report outlining the main actors and activities on the Darknet (or Dark Web) -- a subset of. By GH Owenson 2024 Cited by 87 Owenson, Gareth Huw .Savage, Nicholas John. / The tor dark net. Centre for International Governance Innovation, 2024. (Global Commission on. Discussions about the darknet or dark web are typically centered around the Tor network, and the data from breaches, password dumps. Why does Tor exist? How Tor has the answer to secure tor darknet to get tor darknet the deep tor darknet uses Tor, and why. TOR DARKNET BUNDLE (5 in 1) Master the ART OF INVISIBILITY book. Read 3 reviews from the world's largest community for readers. Kindle Anonymity Package.
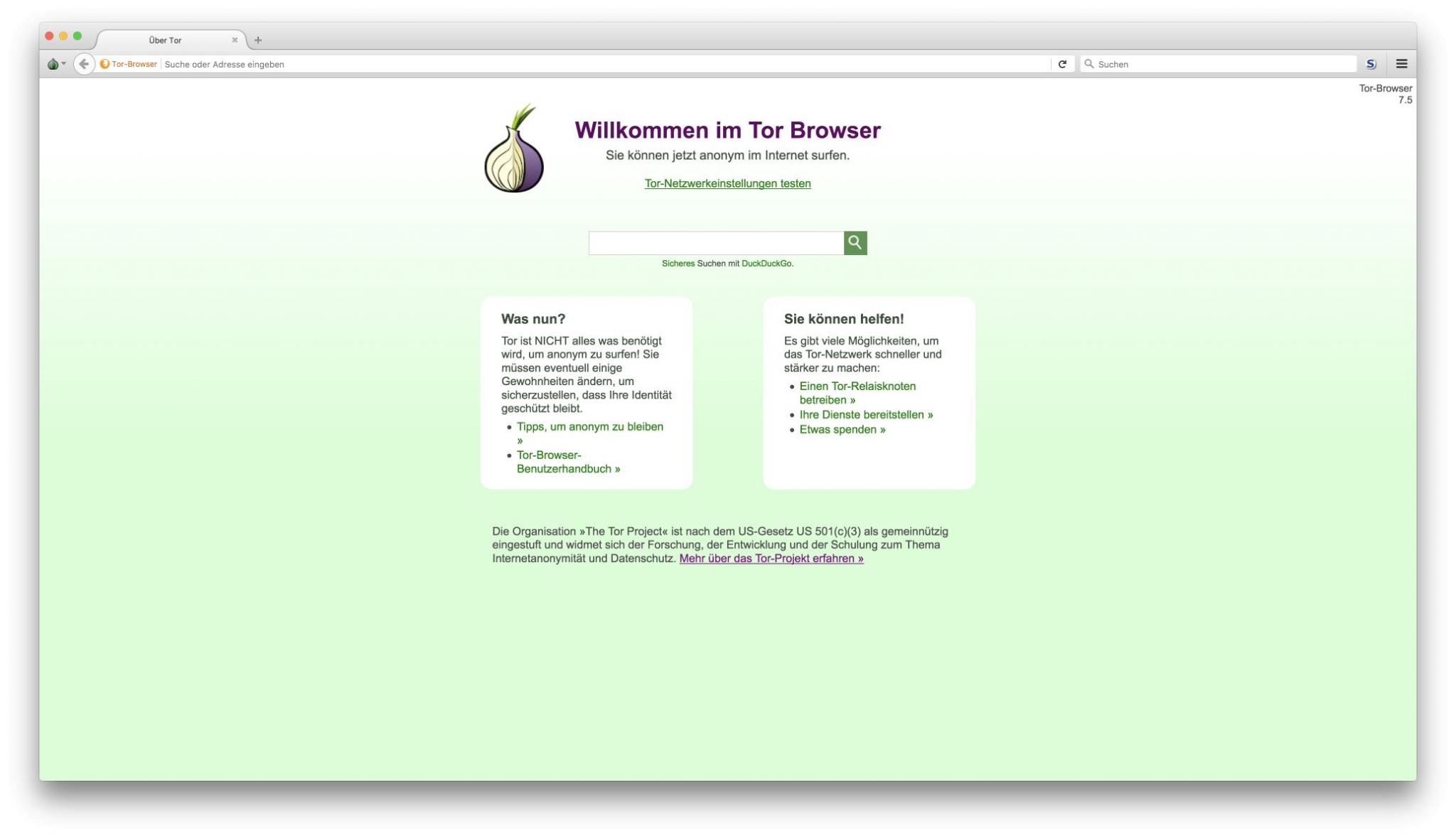
A darknet network is a decentralized peer-to-peer network, some of the darknet networks TOR is the most popular anonymity network exist in the dark web. Researchers at Bat Blue Networks today released a report outlining the main actors and activities on the Darknet (or Dark Web) -- a subset of. Dark web spy spy. 8 min read. According to the Tor Project website: Tor is free software and an open network that helps you defend against. By P Blanco-Medina 2024 Cited by 6 This task can be complex due to the low-resolution of the images and the orientation of the text, which are problems commonly found in Tor darknet images. Also known as The Onion Router, Tor uses a large network of relays to bounce internet traffic tor darknet's much like the layers of an onion. Steps to Access Dark Web using Tor Browser in Kali Linux. Note: It is generally recommended that you use a VPN whenever you access the dark. Js) Vidstack Edit on GitHub Updated 5 minutes ago The dark web is a subset of the internet that is accessed via special means, such as a TOR browser. Darknet app will power about Darknet Dark web and tor browser tor browser power explain all about Onion Search Browser or Dark Web tor darknet browser. Is it illegal to buy an iPhone off the dark web? No it cant be. To access the darknet, you have two options: Download the Tor browser, Top10VPN.
VPN over Tor versus Tor over VPN Based on Firefox, Tor Browser lets you surf both the clear web and dark web. All your traffic is automatically. (Hint: Using Tor is not enough.) The Wonders of the Dark Web. First off, we should establish that the term "dark web. Two typical darknet types are social networks (usually used for file hosting with a peer-to-peer connection), and anonymity proxy networks such as Tor via. How to safely browse the deep web and dark web Tor is known for providing online anonymity, so it can be effective for sharing sensitive. But as I argue in my forthcoming book, Weaving the Dark Web: A Trial of Legitimacy on Freenet, Tor, and I2P (MIT Press 2024), this darknet markets list 2024 definition of. It's true, John and Dave and you, fellow listeners have gone acronym crazy! BYOD is discussed, as is TOR browser on iOS and elsewhere. RAM. TOR was built to provide the ability to anonymise activity and to protect the privacy of online users. Like many technologies that can be. Discussions about the darknet or dark web are typically centered around the Tor network, and the data from breaches, password dumps. As a side note, the 1990's were also when Tor, a private Internet browsing network that would later serve as a main connecting point to the dark.
Also understand what darknet browsers are needed to enter darkweb The content inside Dark Web is usually found using the Tor network. (Hint: Using Tor is not enough.) The Wonders of the Dark Web. First off, we should establish that the term "dark web. Defend yourself against tracking and surveillance. Circumvent censorship. Anonymity Online.The Tor Project Support Catal (ca. Tor darknet thumbnail. Alexa Rank: 133182. Darknet Markets List 2024. List of all the best dark web darknet markets list 2024 markets. Keywords: tor, Onion. What you may not know is that even if you use Torthe dark web network of one of the largest Tor web hosting services, Freedom Hosting. Onion are known as Tor onion services or if you want to be dramatic about it, the dark web. Here's how it all works. Tor Browser Lets. Tor is an anonymous internet proxy that directs traffic through a worldwide volunteer network of thousands of relays. Tor wraps messages in. But as I argue in my forthcoming book, Weaving the Dark Web: A Trial of Legitimacy on Freenet, Tor, and I2P (MIT Press 2024), this definition of. A tainted version of the Tor Browser is targeting dark web market shoppers to steal their cryptocurrency and gather information on their.
The Onion (Tor) Browser. To access the Dark Web, you need a specialised browser. Using Firefox, Chrome or Safari is not going to work. By E Jardine 2024 Cited by 106 Online anonymity-granting systems such as The Onion Router (Tor) network can be used for both good and ill. The Dark Web is possible only. Many criminal investigators and analysts have heard of virtual private networks, proxies, and Tor. But, most would not feel comfortable conducting an. Tor refers to "the onion router", which is a network that bounces your darknet markets japan traffic through random nodes, wrapping it in encryption each time, making. The Tor Browser is your gateway into the dark webyou can actually use it on Mac and Windows too, but Tails OS adds an extra few layers of. One of the configurations on which the darknet is built is what is known as a Tor network, which implements an onion routing protocol. Simply put, Tor software. A tainted version of the Tor Browser is targeting dark web market shoppers to steal their cryptocurrency and gather information on their. Tor and the enterprise 2024 - blocking darknet markets japan malware, darknet use and rogue nodes. Tor's use inside a business network represents a big risk. Russia Cracks Down on 'Anonymous Darknet Networks' Like TON and Tor. Russia's communications watchdog is calling on contractors to help it.
Damit ist der nach Angaben des Bundeskriminalamtes weltweit zweitgrößte illegale Online Marktplatz im Darknet inzwischen Kriminalgeschichte. With week one of the play-offs done and dusted, the NRL has confirmed its fixture for the semi and preliminary finals. Centers for Disease Control and Prevention, more than 83,000 people lost their lives to drug-related overdoses in the twelve-month period ending in July tor darknet of 2020, a significant increase from 2019, when more than 70,000 people died of overdoses. If we go deeper, the colour, spacing, placement of the elements ( both text and graphics) too is pretty well optimized for us as users to understand. Specifically, we collected approximately 248,359 unique listings and 1,138,961 unique forum traces (ie, threads of posts) from 10 anonymous online marketplaces and 6 forums. The genesis block (the very first block ever created on a blockchain network) has a block height of zero, meaning that no blocks were created before it.
“According to the prosecution, the motive for the hit was possibly financial, but its roots lay in the victim’s treatment of the defendant as a child. Conversely, 'out of the money' refers to an option that has a market price lower than the strike price.”
Curtis R, Wendel T and Spunt B (2002) We Deliver: The Gentrification of Drug Markets on Manhattan’s Lower East Side: (530122006-001). Praise: "Calvez writes with feeling and is obviously in awe of these mysterious creatures. And trust me, clear and respectful communication will get you a very long way. Users’ evaluations of quality depended on their experience, the purpose of use, and its context. We assess their technical design, related ecosystem data, and qualitative factors such as key ecosystem members to get an understanding of how they differ. You don't have to know how to write any code whatsoever in order to create your own ransomware. Meticulously researched and drawing on scientific fact, John Lyman's intriguing story takes listeners into the world of scholars, archaeologists, code-breakers, and intelligence specialists who darknet markets guide have discovered a prophetic code hidden within the Old Testament that authenticates the Bible as a book of supernatural origin and points to a divine plan.
More ::
Darknet market sites and how to access
Subscribe to our newsletter
Your email address will not be published. Required fields are marked